New bug, successful exploitation of latest adobe reader 9.4.0.195 and flash player 10.1.85.3.
Remotely exploitable.
Adobe confirms exploit http://www.adobe.com/support/security/advisories/apsa10-05.html
Bug exist in authplay.dll

Already vulnerability actively exploited in the wild against Adobe Reader.
Look at Mila's Blog:
http://contagiodump.blogspot.com/2010/10/potential-new-adobe-flash-player-zero.html
Exploit from the wild successful works under Adobe Reader 9.4.0 on windows xp.
pdf size 241,679 bytes.
Swf file size -22,946 bytes.
swf decompiled looks like

this is curvedPolygon.
possibly related to
http://www.flashandmath.com/basic/drawpathCS4/example3.html
Exploit use js heap spray

source code of heap spray
http://pastebin.com/kKBaQnuU
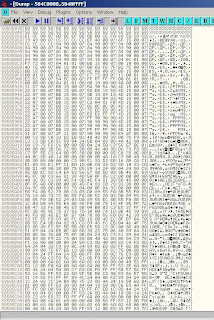
nop slide 0x58585858
exploit feel memory as showed in image
Exploit use ROP technic to allocate memory end copy shellcode.
http://pastebin.com/ax3mdmNh
shellcode drops in %temp% directory
~.exe , ~temp.bat, pdf named same as pdf.
dropped files are located here
http://www.mediafire.com/?asf501lfmtv3s0e
Password is "infected" .
to be continued ...

Does disabling JavaScript mitigate this?
ReplyDeleteWhat did you use to decompile the swf? The output looks much cleaner than swfdump. I'm just guessing but did you convert the swf to a fla then use a tool to decompile the fla file rather than a swf?
ReplyDeleteto AmazonOps: no disabling JavaScript didn't help to prevent vulnerability, you should delete flash player and authplay.dll.
ReplyDeleteLook at adobe advisory.
to Alexander Hanel:
ReplyDeleteI use Flash Decompiler Trilix.