http://contagiodump.blogspot.com/2011/04/apr-8-cve-2011-0611-flash-player-zero.html
http://www.adobe.com/support/security/advisories/apsa11-02.html
Filename: Disentangling Industrial Policy and Competition Policy.doc
Size:176,144 bytes
My analysis of Disentangling Industrial Policy and Competition Policy.doc

File created 04-Apr-2011 9:50 , by user 7 , and company hust
There are no vulnerabilities in MS Office, there is a vulnerability in embeded swf as was described below.
embeded swf file(local name d:\513.swf)
size 10,421 bytes
decoded action script
this is heap spray, allocate memory with nop slide=0x11111111.
and load second swf file.
second swf
size 1,484 bytes
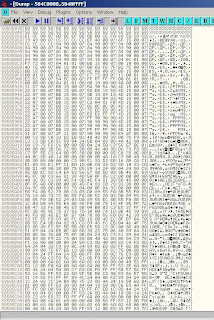
SWFTools>swfdump.exe -D 1.swf
[HEADER] File version: 10
[HEADER] File size: 1484
[HEADER] Frame rate: 24.000000
[HEADER] Frame count: 1
[HEADER] Movie width: 550.00
[HEADER] Movie height: 400.00
[045] 4 FILEATTRIBUTES
[00c] 1447 DOACTION
GetU8() out of bounds: TagID = 12
flasm16win>flasm.exe -d 1.swf
movie '1.swf' // flash 10, total frames: 1, frame rate: 24 fps, 550x400 px
frame 0
00000000 push FALSE, 326943637, 326943739
0000000F oldEquals
00000010 not
00000011 branchIfTrue label2 // offset 1100
00000016 branchIfTrue label1 // offset 24
0000001B constants 'A', 'B', 'C', 'D', 'E', 'F', 'G', 'H', 'I' Declared constant pool length 21 differs from calculated length 20
Disassembly may be incomplete: wrong action length encountered
end // of frame 0
end
crash exist in Adobe Flash Player plugin .
in my test NPSWF32.dll (10.2.153.1)
crash at location 100cfc03
this possibly related to tweet :
call [0x11111110+0x08]
to be continue ...